In today's digital age, data is the lifeblood of organizations. As such, securing that data has never been more crucial. To safeguard sensitive data from unauthorized access, breaches, and other security threats, it's essential to implement robust security measures. This article will offer a few such measures for securing your relational databases.
Access Control
One of the fundamental principles of database security is controlling access to stored data. Implementing strong access controls ensures that only authorized users can interact with the database. This involves assigning unique user accounts with specific permissions based on their roles and responsibilities.
- User Authentication: Enforce strong password policies and use multi-factor authentication to add an extra layer of security. This helps prevent unauthorized access, even if login credentials are compromised.
- Role-Based Access Control (RBAC): Implement RBAC to assign permissions based on users' roles within the organization. This minimizes the risk of users having unnecessary access to sensitive data.
Encryption
Encrypting data at rest and in transit is crucial to protect it from unauthorized access and interception.
- Data at Rest Encryption: Utilize encryption algorithms to secure data stored on disk or in backups. This prevents unauthorized access to the physical storage media, adding an additional layer of protection.
- Secure Sockets Layer (SSL) or Transport Layer Security (TLS): Encrypt data in transit by using SSL or TLS protocols. This ensures that communication between the database server and client applications is secure and cannot be easily intercepted.
Backup and Recovery
A solid backup and recovery strategy is essential to mitigate the impact of data loss or corruption due to security incidents.
- Regular Backups: Schedule regular backups of the database and verify their integrity. Store backups in a secure location separate from the production environment.
- Point-in-Time Recovery: Implement point-in-time recovery mechanisms to restore the database to a specific state before a security incident occurred.
Employee Training and Awareness
Human error is a common cause of security breaches. Educate employees about security best practices and the importance of safeguarding sensitive information. Conduct regular security awareness training to keep employees informed about the latest security threats and best practices. This empowers them to recognize and report potential security incidents.
Real-time Monitoring
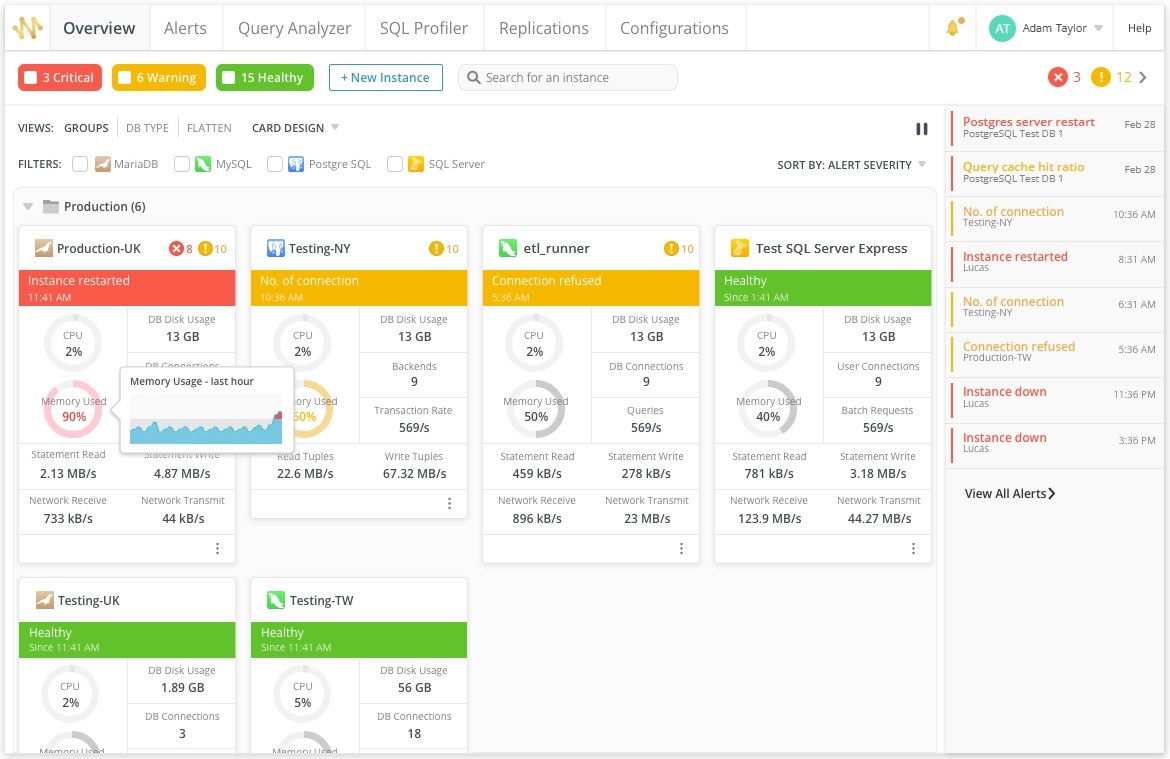
Utilize real-time monitoring tools to track performance metrics and identify anomalies or potential security threats. That's where a tool such as Navicat Monitor 3 can help. It's a comprehensive database monitoring and performance optimization tool designed for MySQL, MariaDB, PostgreSQL and SQL Server, as well as cloud databases like Amazon RDS, Amazon Aurora, Oracle Cloud, Google Cloud and Microsoft Azure. Navicat Monitor 3 offers several features that contribute to the overall security of relational databases, including:
- Real-time Monitoring: Navicat Monitor 3 provides real-time monitoring of various performance metrics, including CPU usage, memory usage, and disk I/O. By staying informed about the database's health, administrators can quickly identify abnormal patterns that may indicate a security incident.
- Alerting and Notification: The tool offers customizable alerts and notifications for performance-related issues. By configuring alerts for specific thresholds, administrators can receive immediate notifications of potential security threats or unusual database activities.
- Historical Data Analysis: The ability to analyze historical performance data helps administrators identify patterns or trends that may indicate security issues. This feature enhances the proactive identification of potential threats before they escalate.
Conclusion:
Securing a relational database is a multifaceted task that requires a combination of access controls, encryption, monitoring, and proactive management. By implementing the security measures outlined in this article and leveraging tools like Navicat Monitor 3, you can fortify your organization's defenses against potential security threats and ensure the integrity and confidentiality of their valuable data.












